Securing Your Application: Best Practices from Day 1
Securing Your Application: Best Practices from Day 1 isn’t just a catchy phrase—it’s a fundamental shift in how you need to approach software development. Cyber threats evolve daily, becoming more sophisticated and targeted. Attackers don’t wait for your application to mature before striking; they probe for weaknesses from the moment you deploy.
The traditional approach of bolting security onto finished applications doesn’t work anymore. You’re essentially building a house and adding locks only after burglars have already mapped every entry point. Application security demands integration from the first line of code you write.
Cybersecurity best practices require you to embed security considerations throughout every stage of the software development lifecycle (SDLC). This proactive stance transforms security from an afterthought into a core design principle. When you adopt secure application development practices from day one, you’re not just protecting data—you’re building trust with users, reducing costly remediation efforts, and staying ahead of threats that could cripple your organization.
The question isn’t whether you can afford to prioritize security early. It’s whether you can afford not to.
1. Understanding the Threat Landscape Early
Threat modeling is your first line of defense in application security. You need to identify potential attack methods, figure out which parts of your application are valuable and should be protected, and understand how attackers might take advantage of your application before you even start coding.
Steps to Create a Web Application Threat Model
Creating a comprehensive web application threat model involves several critical steps:
- Identifying entry points where users or systems interact with your application
- Cataloging data flows to understand how information moves through your system
- Documenting trust boundaries where data crosses from trusted to untrusted zones
- Analyzing potential threats using frameworks like STRIDE (Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, Elevation of Privilege)
The Importance of Risk Assessment
Risk assessment allows you to prioritize which applications need immediate attention. You’ll evaluate each application based on the sensitivity of data it handles, the number of users it serves, and its exposure to external networks. Applications processing payment information or personal health records naturally rank higher on your priority list than internal tools with limited data access.
Catching Security Flaws Early
Finding threats early on can greatly reduce vulnerabilities by fixing security flaws during the design phase—when it costs much less compared to fixing them after deployment. You’re basically making security an integral part of your application’s structure instead of adding it later on.
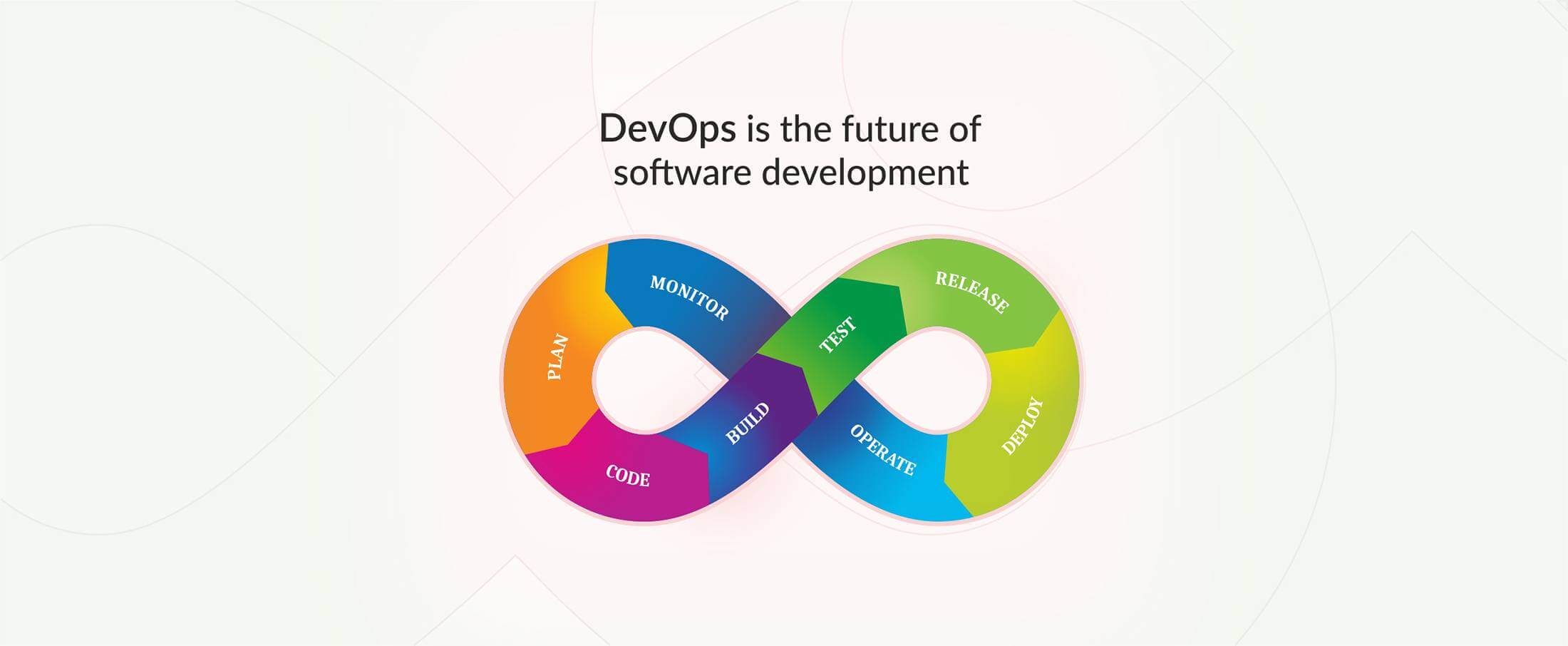
2. Integrating Security into the Software Development Lifecycle (SDLC)
Building security into your development process from the beginning—not bolting it on at the end—transforms how you protect your applications. The secure SDLC approach weaves security checkpoints into every development phase, catching vulnerabilities when they’re cheapest and easiest to fix.
Understanding Shift Left Security
Shift left security means pushing security testing earlier in your development timeline. You’ll want to implement:
- Static Application Security Testing (SAST) – Analyzes your source code without executing it, identifying security flaws like SQL injection vulnerabilities or buffer overflows during the coding phase
- Software Composition Analysis (SCA) – Scans third-party libraries and open-source components for known vulnerabilities, tracking dependencies that could introduce security risks
- Dynamic Application Security Testing (DAST) – Tests your running application from the outside, simulating real-world attacks to uncover runtime vulnerabilities
The Benefits of Automated Security Testing
Automated security testing removes the burden of manual reviews and accelerates your development cycle. Integrating these tools into your CI/CD pipeline means every code commit triggers security scans automatically. You catch issues in minutes, not weeks, and your developers receive immediate feedback to remediate problems before they reach production.
3. Implementing Secure Coding Practices
Secure coding is the foundation of application security, and you need to establish these practices from your first line of code. The most critical aspect is input validation—you must treat every piece of user input as potentially malicious. Validate data types, length, format, and range before processing. Sanitize inputs by encoding special characters and using parameterized queries to prevent SQL injection attacks. For XSS prevention, escape output data and implement Content Security Policy headers.
Hardcoded secrets represent a critical vulnerability you should never introduce into your codebase. Passwords, API keys, and encryption keys embedded directly in source code create easy targets for attackers who gain repository access. Instead, you should:
- Store secrets in environment variables separate from your application code
- Use dedicated secret management tools like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault
- Implement automated secret scanning in your CI/CD pipeline to catch accidental commits
- Rotate credentials regularly and revoke compromised secrets immediately
Code vulnerability prevention requires you to follow language-specific security guidelines and use security-focused linters that identify common weaknesses during development.
4. Access Control and Authentication Best Practices
Authentication is the first line of defense for your application against unauthorized access. To enhance security beyond just passwords, implement multi-factor authentication (MFA). This requires users to verify their identity through multiple methods such as SMS codes, authenticator apps, or biometric data. Many applications have successfully reduced account takeover incidents by over 90% after adopting MFA.
Role-Based Access Control (RBAC)
Instead of assigning permissions to individual users, use role-based access control (RBAC) to structure permissions around job functions. Create roles like “admin,” “editor,” or “viewer” with specific capabilities, making it easier to manage and audit access. For example, when a developer requires database access, simply grant them the “database-developer” role instead of manually setting up individual permissions.
The Least Privilege Principle
Apply the least privilege principle by giving users and services only the resources they truly need. For instance, your web server shouldn’t have write access to configuration files, and your marketing team shouldn’t possess production database credentials. This containment strategy helps limit the potential damage if credentials are compromised—an attacker gaining access to a restricted account won’t be able to move laterally into sensitive systems or data.
5. Data Protection and Encryption Strategies
Data encryption is essential for safeguarding sensitive information within your application. You must implement encryption in two key areas: when data is stored and when it is transmitted over networks.
Data Security at Rest
To secure data that is not actively being used, you need to encrypt the following components:
- Databases
- File systems
- Backup repositories
Use industry-standard algorithms such as AES-256 for encryption. Additionally, never store passwords in plain text—always hash them using bcrypt or Argon2 with appropriate salting techniques. If you are using cloud storage services like AWS S3 or Azure Blob Storage, take advantage of their built-in encryption features by enabling them with a simple configuration change.
Data Security in Transit
When data is being transmitted across networks, it is crucial to protect it using TLS (Transport Layer Security) protocols. Ensure that you configure TLS 1.2 or higher for all your APIs, web services, and database connections. While self-signed certificates may be convenient during development, it is important to use certificates from trusted Certificate Authorities in production environments.
Additional Secure Storage Measures
In addition to encryption, there are other measures you should take to ensure secure storage:
- Implement proper key management using services like AWS KMS or HashiCorp Vault.
- Rotate encryption keys regularly according to your security policy.
- Keep encryption keys separate from the data they protect.
- Apply field-level encryption for highly sensitive data such as credit card numbers or social security numbers.
6. Deploying Protective Technologies
Web application firewalls (WAFs) are your first line of defense against common attack patterns. You can set up WAF solutions such as Cloudflare, AWS WAF, or ModSecurity to block SQL injection attempts, cross-site scripting, and other OWASP Top 10 threats before they reach your application code. These tools analyze HTTP/HTTPS traffic in real-time, filtering out malicious requests based on predefined rules and custom policies you define.
Virtual patching is crucial when you find vulnerabilities but can’t immediately deploy code fixes. Your WAF can implement temporary protective rules that shield the vulnerable endpoint while your development team works on a permanent solution. I’ve used this approach during critical production incidents—it gave us time to thoroughly test patches instead of rushing fixes into production.
Layered defense mechanisms make your security more effective. When you combine WAF protection with input validation, secure coding practices, and encryption, attackers must get past multiple security controls. This strategy means that even if one vulnerability exists, it won’t compromise your entire application, giving you chances to detect attacks at each layer.
7. Continuous Monitoring and Incident Response Planning
Protective technologies alone won’t keep your application secure—you need visibility into what’s happening in real-time. Security monitoring transforms your application from a black box into a transparent system where suspicious activities trigger immediate alerts.
SIEM systems aggregate and analyze security logs from multiple sources, correlating events to identify potential threats before they escalate. Tools like Splunk, IBM QRadar, and Microsoft Sentinel provide centralized dashboards that help you spot patterns indicating compromise. You’ll see failed login attempts, unusual API calls, or unexpected data access patterns that human analysts might miss.
Real-time analysis catches attacks in progress:
- Automated alerts for privilege escalation attempts
- Detection of abnormal traffic patterns
- Identification of data exfiltration activities
- Recognition of known attack signatures
Your incident response plan determines how quickly you contain breaches. Document clear procedures for isolating affected systems, preserving forensic evidence, notifying stakeholders, and restoring services. Assign specific roles to team members and conduct regular tabletop exercises to test your response capabilities under pressure.
8. Regular Security Assessments and Maintenance Activities
Penetration testing is your proactive security approach, mimicking real attacks to find weaknesses before hackers can take advantage of them. You should plan these tests every three months or after significant application updates, involving both internal teams and outside security professionals to get different viewpoints on your security situation.
Security audits work alongside penetration testing by offering thorough evaluations of your security measures, settings, and compliance practices. These audits focus on:
- Checking how users are verified and authorized
- Reviewing how data is encrypted
- Assessing the security of your APIs
- Analyzing any third-party integrations or dependencies
- Evaluating your access control rules
You must consider software dependency updates as crucial maintenance tasks. Weaknesses in libraries and frameworks are responsible for many application breaches. Automated tools like Dependabot, Snyk, or WhiteSource can notify you about vulnerable dependencies, but it’s important to act swiftly and apply patches.
Security maintenance isn’t something you do once—it’s an ongoing responsibility. Cyber threats change every day, with attackers always coming up with new ways to exploit systems. The security measures you had in place six months ago might not be enough to protect against today’s threats, so it’s vital to continuously assess and adapt your strategies to keep your application strong.
9. Reducing Attack Surface by Managing Application Inventory
Your organization’s attack surface expands with every application you deploy, but the real danger often lurks in the applications you’ve forgotten about. Shadow IT—unauthorized applications running outside IT’s visibility—creates blind spots that attackers exploit. You need to maintain a comprehensive inventory of all applications, including those deployed by individual teams without formal approval.
Application retirement plays a critical role in Securing Your Application: Best Practices from Day 1. Unused applications still consume resources and require security patches, yet they rarely receive the attention active systems get. You should:
- Conduct quarterly reviews to identify dormant or redundant applications
- Decommission applications that no longer serve business purposes
- Remove associated user accounts, databases, and API endpoints
- Document the retirement process to prevent accidental redeployment
Limiting exposed services directly reduces potential entry points for attackers. You can achieve this by:
- Closing unnecessary ports and disabling unused features
- Implementing network segmentation to isolate critical applications
- Using API gateways to control and monitor service access
- Regularly scanning your infrastructure for unauthorized deployments
10. Training Development Teams on Application Security Best Practices
Your developers are your first line of defense against vulnerabilities. Secure coding training transforms them from potential security liabilities into security champions who can identify and prevent threats during development.
Establishing a structured training program ensures your team stays current with evolving attack vectors. You need to cover:
- Common vulnerability patterns like injection flaws, broken authentication, and insecure deserialization
- Secure API design principles and data validation techniques
- Proper implementation of cryptographic functions and secure session management
- Threat modeling exercises using real-world scenarios from your application stack
Cybersecurity awareness extends beyond technical skills. You should cultivate a security-first mindset where developers question assumptions, challenge insecure defaults, and proactively consider attack scenarios. Hands-on workshops using vulnerable code samples let your team practice identifying and fixing security flaws in a controlled environment.
Regular knowledge-sharing sessions keep security top-of-mind. When developers understand why certain practices matter—not just what to implement—they make better security decisions independently. You’ll see fewer vulnerabilities reaching production, faster remediation times, and reduced costs from catching issues early in development.
Conclusion
Securing Your Application: Best Practices from Day 1 requires commitment to proactive security at every stage of development. You can’t treat application security as an afterthought—it demands integration from initial design through deployment and beyond.
The most effective application security best practices combine three essential elements: skilled people, robust processes, and appropriate technologies. You need developers trained in secure coding, automated testing tools scanning for vulnerabilities, and WAFs protecting production environments. Regular assessments through penetration testing and security audits keep your defenses sharp against evolving threats.
Proactive security means continuous education for your teams, timely patching of dependencies, and maintaining visibility across your entire application portfolio. When you embed these practices into your development culture, you build applications that withstand today’s sophisticated cyber threats while adapting to tomorrow’s challenges.
- Application Security Best Practices
- Cybersecurity in SDLC
- Proactive App Protection
- Secure Software Development
- Shift Left Security
13 Oct 2025